From Vulnerable Words to Unhackable Hardware: A New Era of Crypto Backup
Imagine writing your banking PIN on a piece of paper and hiding it, knowing that anyone who finds that single sheet of paper can drain your entire account. This is the fundamental risk millions of cryptocurrency users accept every day with traditional seed phrase backups. These 12 or 24-word recovery phrases, while functional, represent a critical point of failure in digital asset security.
Tangem Card redefines cryptocurrency backup from the ground up. Instead of relying on vulnerable words written on paper or stored digitally, Tangem uses a secure hardware-to-hardware cloning process that never exposes your private keys. For anyone seeking true peace of mind in self-custody, understanding this process is crucial. This article will demystify exactly how Tangem Card creates and backs up your cryptographic keys with military-grade security, eliminating the single biggest vulnerability in personal crypto storage.
Why Seed Phrases Are the Weakest Link (And What Tangem Offers Instead)
Before diving into the “how,” it’s essential to understand the “why.” Traditional seed phrases are a form of “something you know” security. Their vulnerability is twofold:
- Exposure Risk: If seen, photographed, or digitally intercepted during creation or storage, they are immediately compromised.
- User Error: Loss, water damage, or simply misplacing the paper leads to permanent asset loss.
Tangem Card replaces this with a “something you have” model. Your access is tied to a physical, secure chip in your possession. The backup process doesn’t create a readable secret; it creates an identical, secure physical clone. This shifts security from protecting information (words) to controlling access to a specific, authenticated device.
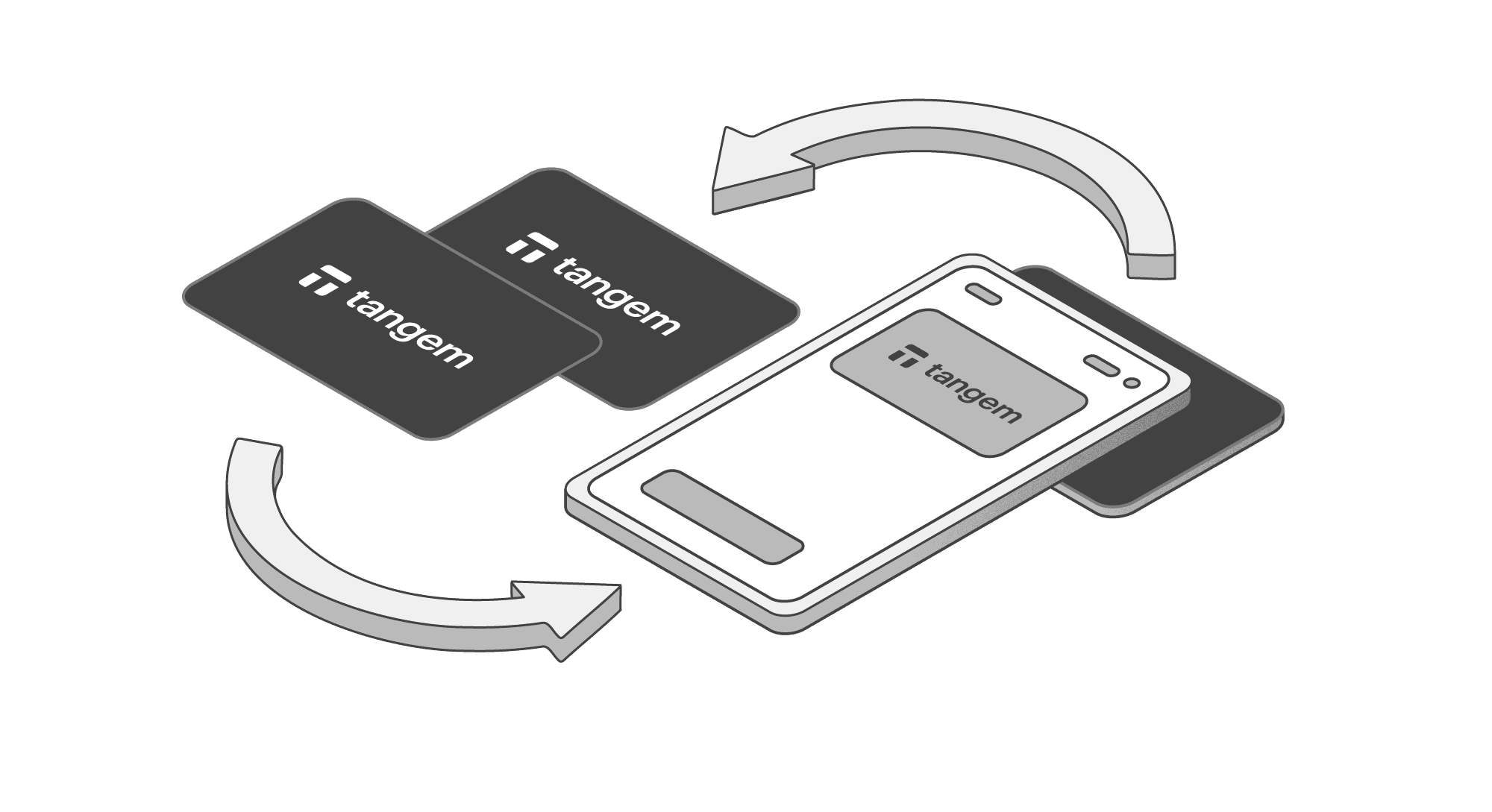
The Tangem Backup Process: A Step-by-Step Journey
The magic of Tangem happens in a multi-layered cryptographic handshake between cards. Here’s how it works in practice, from unboxing to secured backup.
Step 1: A Truly Blank Slate – Generation in Isolation
When you receive your Tangem Card pack, the cards are cryptographically blank. No private key exists anywhere in the world for your future wallet until you activate it. This is a vital starting point for trust. During the first tap on your smartphone to activate, the secure chip inside the primary card uses a certified True Random Number Generator (TRNG) to create your unique private key entirely inside the card’s secure element. At this moment, only one copy of this key exists in the universe—inside that single card.
Step 2: The Secure Handshake – Proving “You Are a Tangem”
When you initiate a backup by tapping a new, blank card, the two cards must first prove to each other that they are genuine Tangem devices. This is called mutual authentication.
Each card has a unique, factory-installed cryptographic identity (a key pair: Kcardpriv/Kcardpub). This identity is signed by Tangem’s own secure manufacturer key, creating a digital certificate. Think of it like a passport issued by a trusted government (Tangem).
During backup, the cards exchange these “passports” and use them to verify each other’s authenticity through a cryptographic chain of trust. If either card fails this verification, the process halts immediately. This prevents any fake or tampered device from ever receiving a key.
Step 3: Creating a Secret Tunnel – The Diffie-Hellman Key Exchange
Once authenticated, the cards need a secure way to communicate the private key. They cannot just “shout” it across, even to a trusted peer. To solve this, they perform a classic yet brilliant cryptographic maneuver: the Diffie-Hellman key exchange.
In simple terms, each card generates a new, temporary key pair. They publicly exchange only the public halves of these keys. Using their own private half and the other card’s public half, each independently calculates an identical shared secret key (Ktrans). The beauty is that this shared secret was never transmitted—it was mathematically derived simultaneously by both parties. An attacker monitoring the entire communication would see only the public keys and could never derive the shared secret.
Visual Aid: Imagine two people publicly agreeing on a shared paint color by each mixing their own secret color with a common public color. They end up with the same final color, but no observer can figure out their original secret ingredients.
Step 4: The Encrypted Transfer – Cloning the Key
Now, with a shared secret key (Ktrans) known only to the two authenticated cards, the primary card encrypts the user’s private key. It packages this encrypted data and sends it to the backup card. The backup card uses its identical Ktrans to decrypt the package and write the private key into its own secure element.
The private key is never exposed in a readable form. It exists only in encrypted form during the brief transfer, secured by a key that was never itself transmitted. After this single operation, the card’s firmware permanently disallows initiating another backup, strictly controlling the number of clones.
Tangem vs. Traditional Backup: A Clear Comparison
| Security Aspect | Traditional Seed Phrase Backup | Tangem Secure Card Cloning |
|---|---|---|
| Backup Form | Words on paper or digital file. | Physical duplicate of a secure chip. |
| Primary Risk | Visual/digital exposure and theft. | Physical loss of all cards (mitigated by using 2-3 backups). |
| Transfer Process | User manually transcribes words, risking exposure. | Fully automated, encrypted chip-to-chip transfer. |
| During Backup | Key is visible/known to the user. | Key is never exposed outside the secure element. |
| Verification | User must check words manually. | Cryptographic mutual authentication between devices. |
Practical Benefits for the Everyday User
For someone holding cryptocurrency in New Zealand or anywhere else, this technology translates to tangible benefits:
- Error-Proof: No handwriting mistakes, incorrect word order, or misplacement of a single word in a 24-word list.
- Fast Recovery: Losing your primary card? Simply tap your backup card to your phone to regain instant access—no tedious 24-word re-entry.
- Inheritance Planning Made Simple: Securely give a backup card to a trusted family member with instructions, creating a robust inheritance plan without them needing to understand complex seed phrase management.
- Peace of Mind: The technical guarantee that your key cannot be stolen via malware, screen recording, or prying eyes during the backup process.
Conclusion: Embracing a Simpler, Safer Standard
The Tangem Card’s backup method isn’t just an incremental improvement; it’s a philosophical shift in personal crypto security. It moves the responsibility from the user’s ability to guard a secret to the device’s ability to securely clone itself.
By leveraging hardware-based mutual authentication and the timeless Diffie-Hellman key exchange, Tangem has effectively made the dangerous and user-unfriendly seed phrase obsolete for its users. For Kiwi investors and crypto enthusiasts looking for a way to secure their digital future that is both radically secure and remarkably simple, the Tangem Card offers a compelling and next-generation solution. It provides the ironclad security of cold storage with a user experience that finally feels native to the 21st century.
Ready to move beyond the risk of seed phrases? Explore the Tangem Card and experience the confidence of true hardware-secured cryptocurrency backup.